Programming and Computer Science
Nobody likes to fix the mistakes another person has made due to incompetence, laziness or simply by accident. But when you yourself are that person...
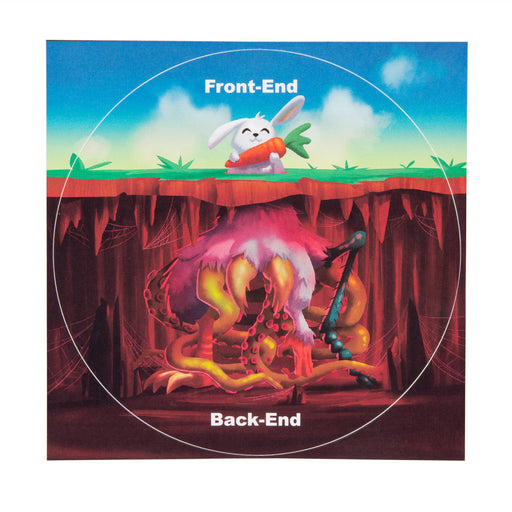
View full detailsAs we all know, silent waters run deep. While software development does not exactly have anything to do with water, the basic principle of the sayi...
View full detailsDas Keyboard 6 Professional is the new generation of the successful and high-quality mechanical keyboards from Das Keyboard. With its stylish and ...
View full detailsAs we all know, hindsight is 20/20. This universally applicable wisdom can also be used to describe informatics, especially debugging (i.e. testing...
View full detailsEven a computer scientist/genius/geek/nerd (delete as appropriate!) has to take a vacation every now and then. He/she leaves the familiar lab, offi...
View full detailsSometimes a simple card game is the best pastime. You know, those times when you're forced to de-digitise, or because of those slow university or w...
View full detailsIf one were to believe the genre legends Run DMC, hip-hop really does have one thing in common with informatics: It's tricky! While the trio of Run...
View full detailsLayer 8 of the OSI model for network protocols is almost exclusively used in a joking manner to imply that most problems are not problems of the sy...
View full detailsHave you ever thought about the proper way to drink coffee? Sure, you might think: "Pour coffee into the mug, lift the mug, drink, repeat as necess...
View full detailsAs we all know, still waters run deep. While software development does not exactly have anything to do with water, still the basic principle of the...
View full detailsNobody likes to fix the mistakes another person has made due to incompetence, laziness or simply by accident. But when you yourself are that person...
View full detailsBasically, programming has a lot in common with Lego: on the one hand, it's worth starting at a young age (keyword: practice makes perfect), and on...
View full detailsBasically, programming has a lot in common with Lego: on the one hand, it's worth starting at a young age (keyword: practice makes perfect), and on...
View full detailsTurns out that most nerds do actually care about nature and know a lot about the evil “outside world”. So much so that even parts of the Unix archi...
View full detailsIf there is any profession entirely deserving of their own drinking song, it’s programmers.The so-called “Programmer’s Drinking Song”, a modificati...
View full detailsImagine that you’ve just created a model that allows different technical systems to communicate with each other and that features different layers ...
View full detailsThere are a few unwritten rules everybody in IT should always follow. And trust us, if you decide to ignore these rules, you definitely won't want ...
View full detailsEveryone who speaks a language with special characters knows the problem: Wrong encoding.
Something you may not know is that computer scientists have to deal with all sorts of trees. Quite often, the most common being the so-called binar...
View full detailsOne nice aspect of mastering a language that not everyone understands is the possibility of being able to make a lot of inside jokes. This is espec...
View full detailsMechanical keyboards are usually a double-edged sword for Mac users, as they often only have the labeling for the PC. Not so with Das Keyboard MacT...
View full detailsComments in code are massively overrated. Those who are in the know don't need extra explanations.
When programmers have worked too long on a project, or when you ask them how the code they worked on actually functions, their favorite answer will...
View full detailsThe word 'hacker' in Japanese, on a T-shirt. The characters are pronounced "hakka" (with a short pause between the k: "hak...
View full detailsLook again!Even on t-shirts, the number of bugs increases by the day. All getDigital t-shirts are of course way past the beta phase ;)
This board game is probably not the number one choice for adult programmers of this world, but it is something the children might get a lot out of....
View full details"Too many cooks spoil the broth!" - a principle that not only applies in the kitchen but also the world of IT. When it comes to identifying former ...
View full detailsOn January 19, 2038, exactly on 03:14:07 (GMT) the 32-bit Unix time variable will be completely filled!Unix-like systems store the time as the numb...
View full detailsLinux - The choice of the GNU generation.
This shirt based on the jurassic park logo is a tribute to all the brave admins combating outdated systems, inexplicable server failures and of cou...
View full detailsAt times, we reach the point where our brain just refuses to function properly and even the simplest tasks are impossible to complete. Most program...
View full detailsAll users of a unix-like operating systems (Linux, Mac, BSD, etc) should know what a fork bomb is. A fork bomb is a program which creates so many c...
View full detailsProgrammers who use pointers should be careful because they aren't far away from hell ;) At least that's what the 2nd of the 10 commandme...
View full detailsWhat's the trick behind all the software and where does it come from? That's what we asked ourselves and then we went on a investigation....
View full detailsIt's safe to say that without IT specialists, the world as we know it could hardly function. Most aspects of our lives, whether we realize it or no...
View full details